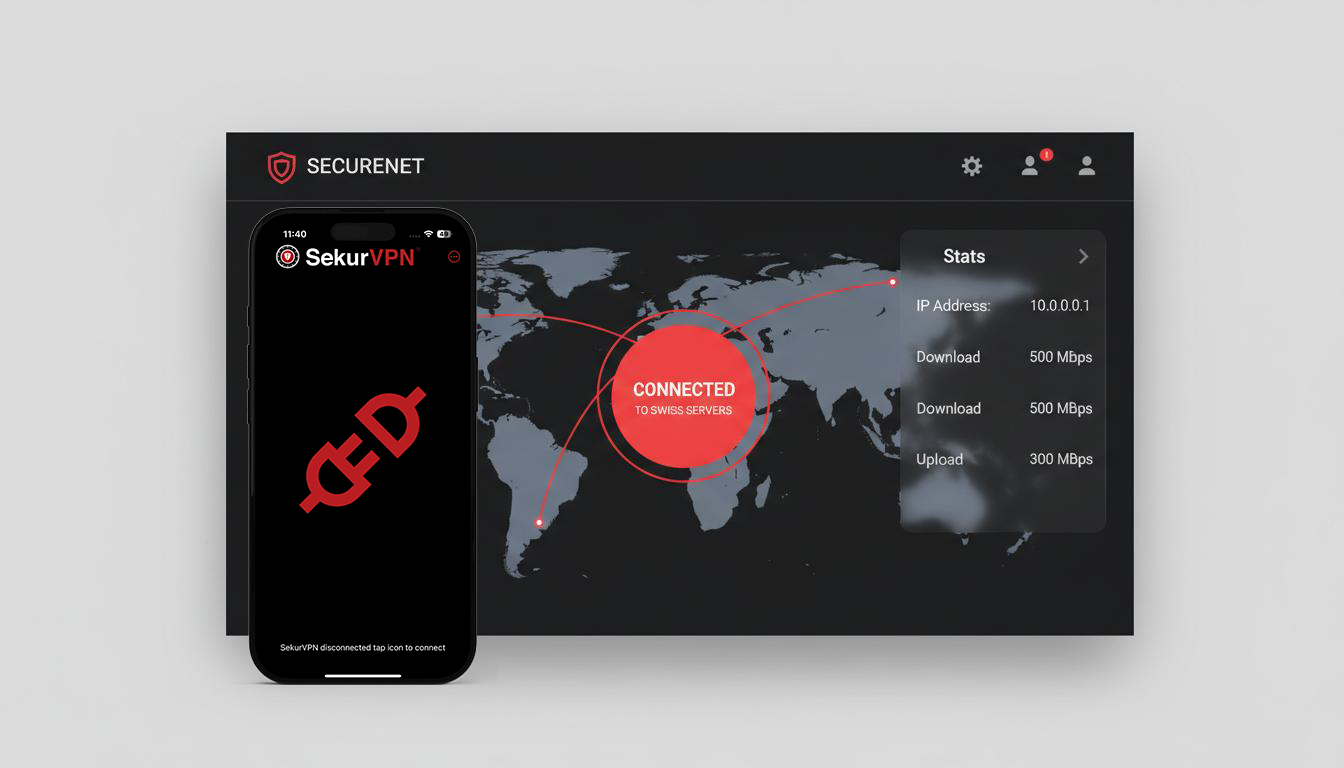
A controlled network access layer designed to remove exposure from public internet infrastructure. Traffic is routed through Swiss-hosted systems under Sekur control, reducing visibility, tracking, and third-party dependency. No tracking. No telemetry. No external visibility.
Swiss Node Active
IP: 185.XX.XX.XX
SekurVPN establishes a controlled network path, removing visibility from public infrastructure before communication even begins.
Operational Outcomes Across High-Trust Environments
Government & Federal Agencies
Secure network access without reliance on third-party infrastructure or public routing layers. Operational traffic remains contained within a controlled Swiss-hosted environment, reducing external visibility and jurisdictional ambiguity.
Defense & Intelligence Coordination
Network-level control that limits exposure of access patterns, locations, and communication timing. Supports secure coordination without dependency on telecom-linked identity or observable traffic paths.
Law Enforcement Operations
Field and investigative teams operate without exposing location, access points, or behavioral patterns through standard network channels. Reduces traceability during sensitive operations.
Diplomatic & International Engagements
Cross-border communications conducted without reliance on local infrastructure or externally monitored networks. Maintains consistency of network presence and reduces exposure across jurisdictions.
Regulated Industries (Finance, Legal, Healthcare)
Network access aligned with strict data handling and residency expectations. Reduces exposure from tracking, monitoring, and third-party infrastructure dependencies.
In these environments, risk is not limited to data. It includes who connects, from where, and when. SekurVPN removes that layer of exposure.
Core Functions
Swiss-Jurisdiction IP Masking
Routing all traffic through 100% proprietary Swiss hardware to ensure data residency.
Zero-Telemetry Infrastructure
A strictly non-logging environment that eliminates the digital footprint.
Signature Neutralization
Complete suppression of telemetry and diagnostic data to ensure operational anonymity.
Cross-Platform Enterprise Integration
Seamless secure access across mobile and desktop operational theaters.
HeliX Encryption
Multi-layer 2048-bit tunnel encryption. Post-quantum resistant. Keys generated and rotated within contained environment.
Contained Within Your Infrastructure
SekurVPN operates as a contained subsystem within defined organizational boundaries. Network access controlled by designated authority. No external dependencies. No shared infrastructure.
- Deployment within organizational device management
- Centralized configuration distribution
- Administrative control over endpoint access
- Audit logging for compliance review
- API access for automated provisioning
SekurVPN
Contained Network Access
SekurVPN: Contained Network Access
Commission deployments based on operational scale and network coverage requirements.
Private
Single-user network access control
Swiss-only routing
No traffic logging
- 5 Devices per account
- Proprietary HeliX protocol + OpenSSL 2028bit
- 2 Factor authentication
- Swiss IP only
- High-speed servers 10Gbps
- No user tracking
- No data mining
- Split tunneling
- Antivirus
- Unlimited data
Operational
Team network access under policy control
Consistent routing across users
No telemetry collection
- 5 Devices per account
- Proprietary HeliX protocol + OpenSSL 2028bit
- 2 Factor authentication
- Swiss IP only
- High-speed servers 10Gbps
- No user tracking
- No data mining
- Split tunneling
- Antivirus
- Unlimited data
- Admin onboarding
Command
Organization-wide network governance
Centralized access control
Enforced routing and monitoring
- 5 Devices per account
- Proprietary HeliX protocol + OpenSSL 2028bit
- 2 Factor authentication
- Swiss IP only
- High-speed servers 10Gbps
- No user tracking
- No data mining
- Split tunneling
- Antivirus
- Unlimited data
- Admin onboarding
- Company Directory
- Password policies
GSA Schedule Availability
Sekur solutions are available through approved GSA procurement channels for eligible government organizations.
High-Volume Deployment & Custom Architecture
For organizations requiring multi-departmental integration, air-gapped configurations, or GSA-schedule procurement. Tailored security posture for defense, government, and regulated industries.
Initiate Strategic ConsultationStrategic Volume Licensing: Tiered pricing for 500+ seat deployments
White-Glove Migration Concierge: Full-spectrum transition from legacy VPN infrastructure
On-Premise Integration: Air-gapped deployment within defined perimeters
Dedicated Liaison: Direct access to Sekur technical leadership
Private communications.
One contained environment.
Written, verbal, and visual communication operate within the same controlled infrastructure. No external routing, no shared cloud, no fragmented systems.
Built for organizations where communication integrity directly impacts operational continuity and decision-making under pressure.
SekurMail
Controlled email
SekurMessenger
Secure messaging
SekurVPN
Private network access
Voice
Encrypted voice calls
Video
Secure conferencing
- All channels unified
- Single infrastructure
- No third-party routing
- Administrative control
- Swiss sovereign hosting
On-Premise Deployment
Deploy within your own infrastructure with full administrative control. No external cloud, no third-party routing. Communication remains contained within your operational environment.
Explore deployment optionsEstablish Procurement Channel
Initiate architectural review, obtain deployment specifications, and establish institutional procurement protocols.